On Monday April 7, 2014, a security vulnerability known as “Heartbleed” was publicly disclosed. This vulnerability allows malicious persons to access information which was transmitted between computers using a specific implementation of Secure Sockets Layer (SSL) communication. SSL is primarily used to secure communications between computers and secure web sites, but the protocol may also be used in other applications.
Does this mean your information has been compromised? Not necessarily, but it is estimated that two-thirds of the world’s web servers are vulnerable, or were vulnerable and have already been patched to remedy the problem. It is highly recommended to assume that web sites you use may have had information compromised.
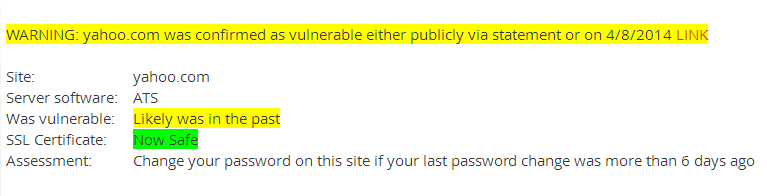
How can I tell if a web site is vulnerable? https://lastpass.com/heartbleed/ is a web site which will check a web site for the vulnerability. This site will indicate whether the site of concern has the vulnerability, or if it was known to have had the vulnerability, its current status. Example output when testing Yahoo.com:
What should I do?
- Check the status of web sites you use. Many sites are publishing notices of their status.
- When you have verified that the site is either not vulnerable, or has corrected the vulnerability, CHANGE YOUR PASSWORD ON THE SITE.
- Do not use the same password for multiple web sites. If a hacker obtains your multiple use password, they then may gain access to any account using that password.
- Use a secure password keeper program to generate unique passwords for each site, and securely record the passwords for your access. LastPass, KeePass, and Dashlane are examples of these products.
Is *my* web site vulnerable? The vulnerability is caused by a problem in a piece of software used by developers. The OpenSSL software components v1.0.1-v1.0.1f are known to be vulnerable. OpenSSL is primarily used in nginx and Apache Linux web servers. Microsoft IIS web servers do not use OpenSSL.
OpenSSL v1.0.1g has corrected the vulnerability. Check OpenSSL version on Linux machines with this command: “openssl version –a”
SSL Certificates: Sites which were vulnerable should also revoke, then reissue, their SSL certificates used in their web servers AFTER updating the OpenSSL libraries. The LastPass.com/heartbleed web site will indicate when the site’s certificate was issued. If a site does not reissue their SSL certificate(s) after remediation of the vulnerability, confidential information is still at risk.
Some web sites that have confirmed they were vulnerable:
- Tumblr
- Google (Gmail, YouTube, Wallet, Play, Apps, App Engine)
- Yahoo
- Etsy
- GoDaddy
- Intuit (Turbotax)
- Box.com
- Dropbox
- GitHub
- IFTTT
- Minecraft
- OKCupid
- SoundCloud
- SpiderOak
by Keith Rainey – Senior Systems Engineer
